add kubeadm install
Showing
docs/16.用 kubeadm 搭建集群环境.md
0 → 100644
docs/17.安装 Dashboard 插件.md
0 → 100644
docs/images/dashboard-login.png
0 → 100644
124.1 KB
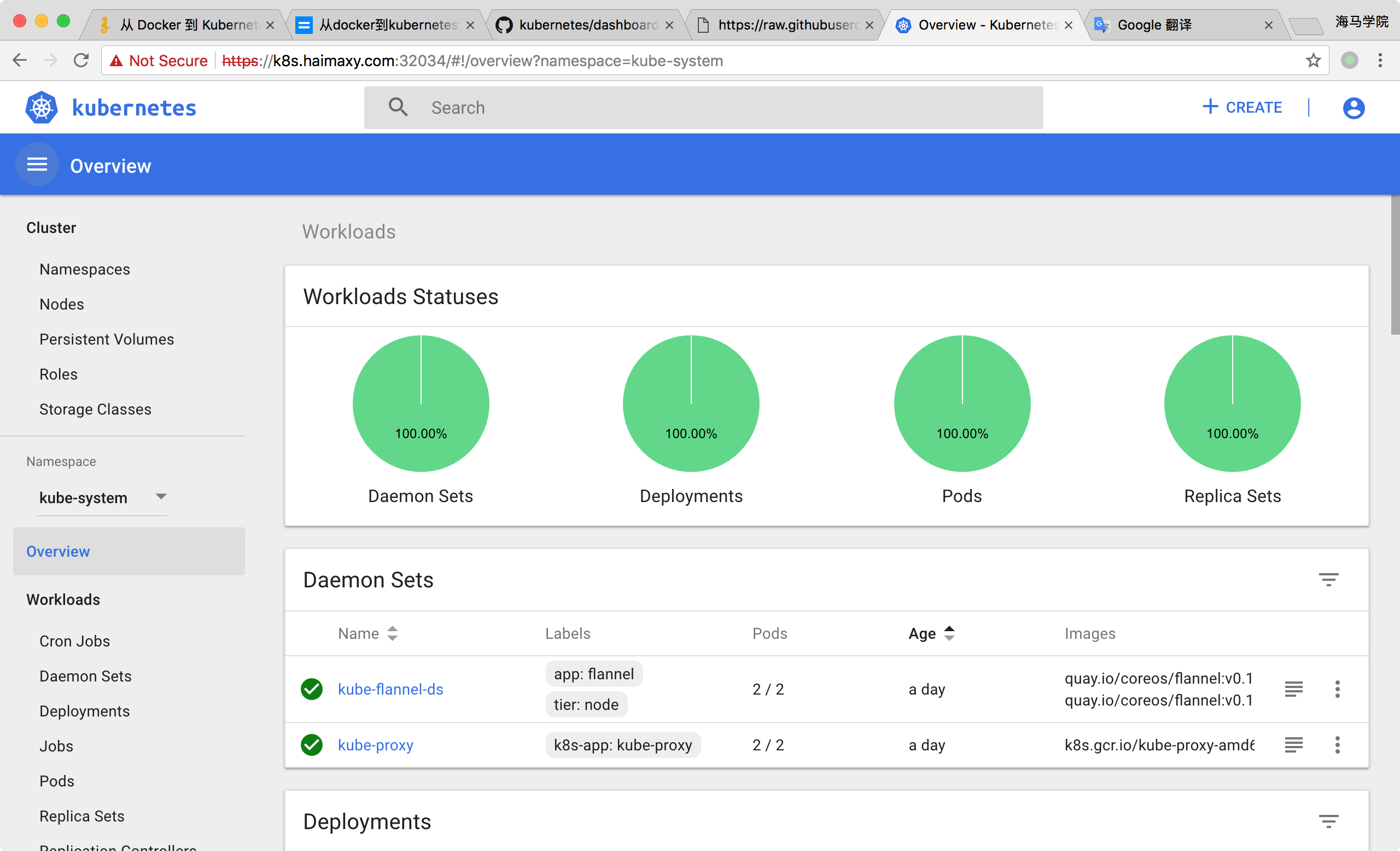
docs/images/dashboard.png
0 → 100644
345.8 KB
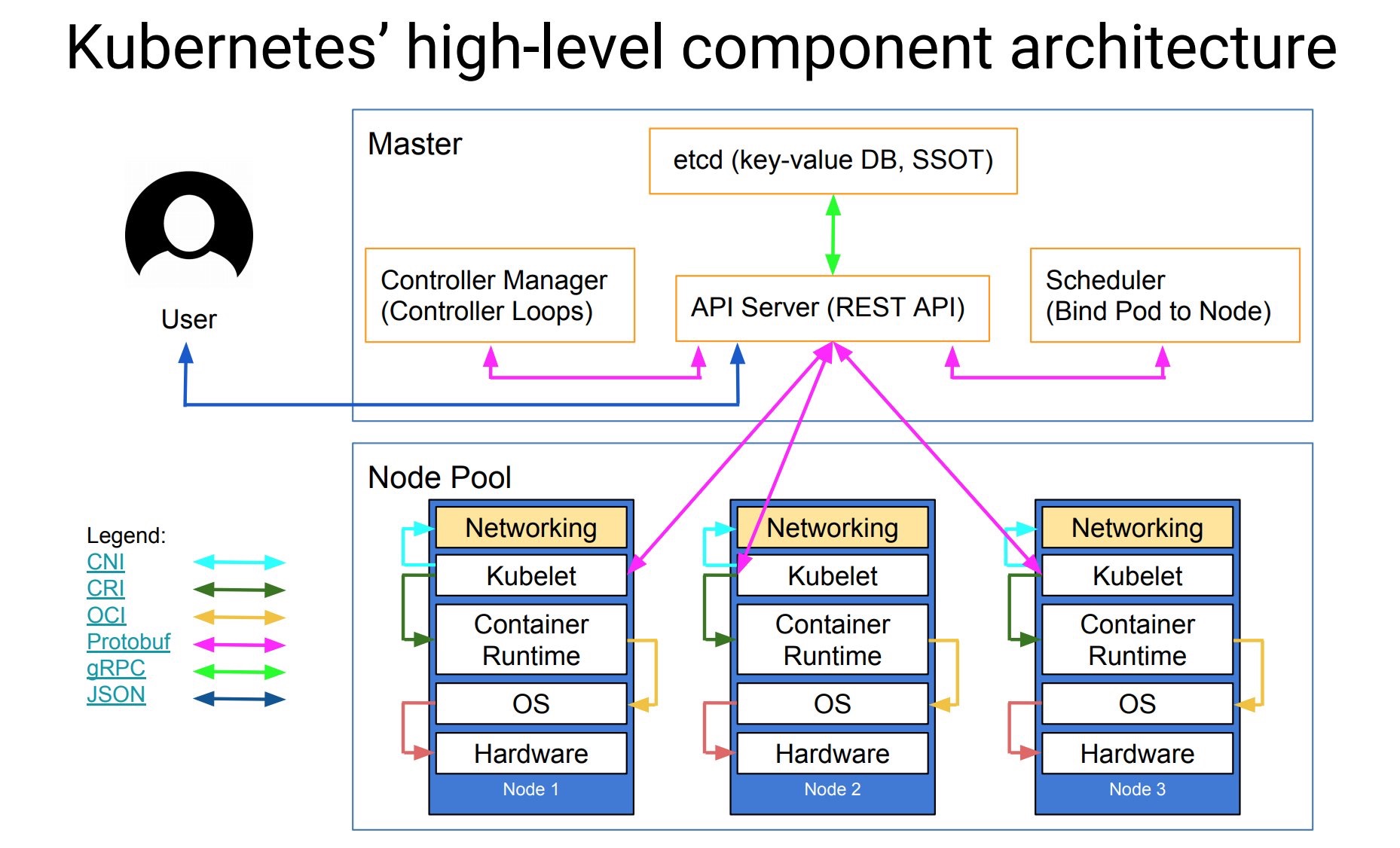
docs/images/k8s-structure.jpeg
0 → 100644
322.7 KB
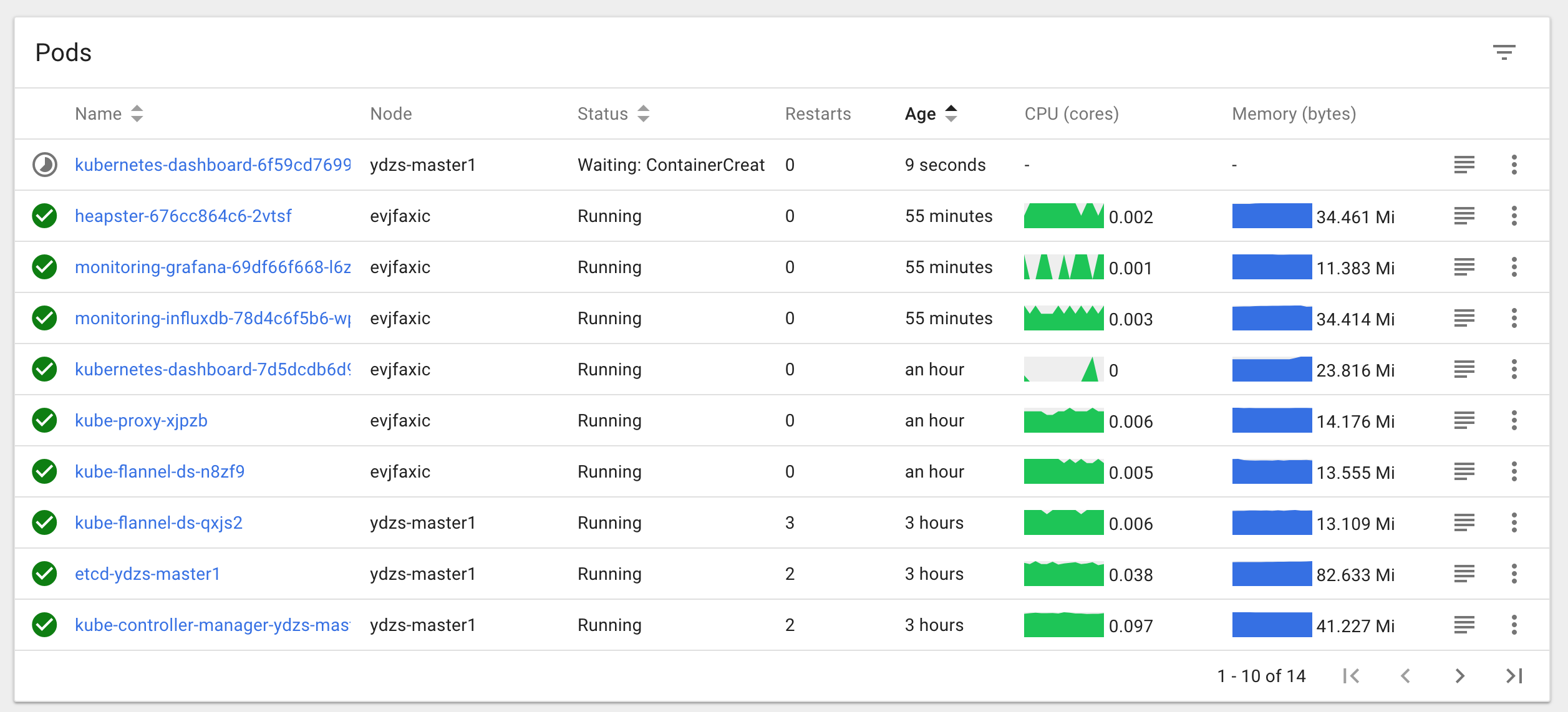
docs/images/kubeadm-dashboard.png
0 → 100644
167.2 KB